Definition of cyber risk and its importance
Cyber risk is the chance of loss caused by a cyber attack or data compromise (e.g., breach or accidental loss) caused by cyber threats or vulnerabilities in networks and digital systems. Included in cyber risk are the potential consequences and the likelihood that a cyber attack will be successful. Cyber risk management involves IT and security teams as well as non-technical areas of an organization, such as finance and supply chain teams.
Don’t ignore a root cause of cyber risk; when it comes to security, companies must start with protecting digital identities.
Because of the far-reaching implications of cyber risk, it is considered to be of the utmost importance for organizations. When cyber risks are exploited, the results include data loss, financial loss, operational disruption, loss of productivity, and reputational damage.
The broad scope of cyber risks also makes it an important issue. Cyber risk vectors range from malicious activities, such as ransomware and other malware, to poor compliance management that creates vulnerabilities that can lead to legal actions and fines.
A simple formula illustrates cyber risk
Potential Impact of a Threat
+
Likelihood of Exploitation
=
Cyber Risk
Cyber risk exposure is usually associated with cyber criminals and cyber attacks, but it can also be accidental. For instance, an employee may inadvertently expose sensitive data by accidentally sending an email to the wrong person. IT issues, such as unpatched systems, open ports, misconfigurations, or vulnerability in third-party software or systems, can also cause it.
Cyber threats and cybersecurity challenges
Cyber threats continue to get more complex and difficult to combat. The rise of remote work and cloud-based systems has exponentially expanded organizations’ attack surfaces and increased cyber risk exposure.
Attackers are highly adept at finding weaknesses and exploiting them. Endpoint, mobile, and IoT (internet of things) devices are often targeted, as they are considered a weak link in an organization’s security and a path to access data and other resources. In some cases, cloud-based collaboration platforms are being used to launch social engineering campaigns that avoid malware and phishing prevention systems used to protect email systems.
Complacency is also a factor that contributes to the efficacy of cyber threats. When organizations have fulfilled their compliance obligations, many believe that this puts them out of the reach of cyber attackers, but this is not the case.
While compliance requirements elevate an organization’s overall security posture, cyber risk remains, and organizations must remain vigilant.
Several of the cybersecurity challenges that organizations face despite valiant efforts to shore up security systems are:
- 5G networks—compromised to gain access to data collected and stored on devices
- Generative AI—used to create highly targeted campaigns, including phishing and deep fakes to compromise accounts and gain unauthorized access
- Mobile malware—designed to exploit inherent weaknesses in mobile devices and their communication protocols (e.g., Wi-Fi and Bluetooth)
- Ransomware attacks—targeting critical business areas
Common cyber risks and their impacts
There are a near-infinite number of cyber risks—some general and others applicable to specific industries or types of users. Commonly seen cyber risks include the following; understanding these can help identify more nuanced cyber risks.
API vulnerabilities
The extensive use of application programming interfaces (APIs) to connect applications and systems creates cyber risks. Top API vulnerabilities that create cyber risk include broken object-level authorization, inadequate user authorization, injection attacks, excessive data exposure, lack of rate limiting, and insecure direct object reference (IDOR). These, along with insecure coding practices, make APIs a significant cyber risk.
Cloud vulnerabilities
Gaps in cloud computing environments create cyber risks that cyber attackers exploit to gain unauthorized access, disrupt services, and steal data. The most common cyber risks associated with cloud environments are human errors and misconfigurations.
Compliance deficiencies
Failure to comply with the security requirements set forth in regulations and standards not only puts an organization at risk for penalties but leaves gaps in security. The security measures that come with these rules reflect best practices designed to address known attack vectors. Cyber risks associated with compliance deficiencies range from exposure to malware and ransomware to phishing attacks and DDoS attacks.
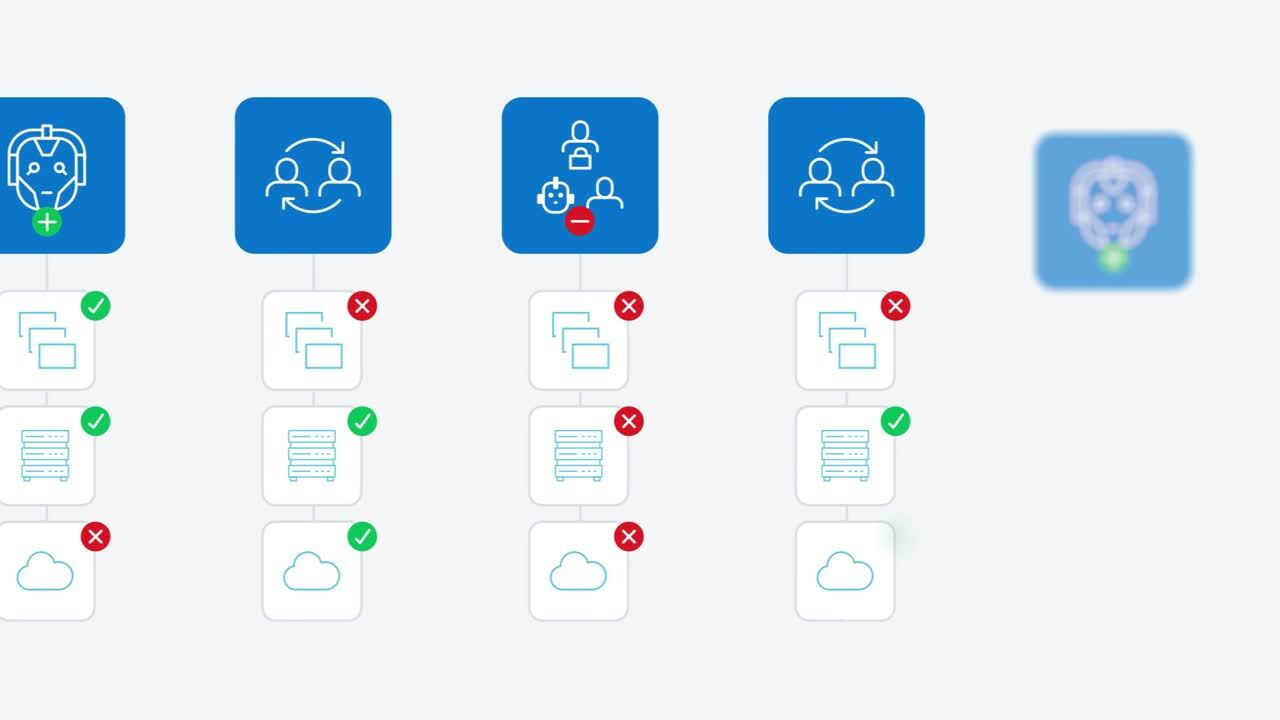
Ineffective access management
A number of cyber risks are associated with ineffective access management. Among the most common access management issues are granting users access to unauthorized data, allowing logins from unauthorized IP (internet protocol) addresses, lack of visibility into user access privileges, and poorly defined access policies.
Insider threats
Insider threats are a serious cyber risk as they result from internal users with authorized access privileges. These are usually associated with malicious activities, such as disgruntled employees, maligning systems, exfiltrating data, or being tricked or coerced into performing misdeeds on behalf of an external cyber criminal. In other cases, internal users simply make mistakes, sharing sensitive information accidentally or losing a device, which is then compromised.
Insufficient data security
Data security lapses can occur in a number of ways. Failing to encrypt sensitive data at rest and in transit exposes it to unauthorized access if the data is intercepted or if a cyber criminal gains access to the data where it is being stored. Another data security issue is caused by data leakage, where sensitive data is exfiltrated.
Lack of visibility
With organizations using many distributed applications and systems, often through the cloud, IT and security teams struggle to gain comprehensive visibility. This leads to a number of elusive vulnerabilities as IT and security teams have difficulty identifying, contextualizing, prioritizing, and mitigating because they cannot monitor many of these tools.
Misconfigurations
Vulnerabilities and misconfigurations in code, especially infrastructure as code or IaC, drive cyber risk in applications and systems. Misconfigurations are often found in containers, virtual machines, and serverless environments, which are difficult for IT and security teams to see and manage.
Poor identity and access management
A number of cyber risks are the result of poor identity and access management policies and enforcement. Access management issues that drive cyber risk include a lack of visibility into identities and associated access privileges, weak authentication, poor password protocols, policy misconfigurations, and not having a standardized, automated process for managing identity lifecycles.
Shadow IT
With the easy accessibility of cloud services and applications, users frequently create and use accounts without the knowledge of IT and security teams. Lacking visibility into these creates security gaps that cause cyber risk. The biggest cyber security risk is data loss caused by users storing sensitive information without proper security and sharing sensitive information with unauthorized parties.
Third-party vendor risk
Third- and fourth-party vendors are responsible for significant cyber risk as they often have access to sensitive data and systems but may not have the level of security necessary to protect them properly.
Consequences of cyber threats on businesses
When considering the impact of cyber risks, an understanding of who is behind the threats can explain what the effects will be if exploits are successful. Several of the common attack profiles and their motivations are as follows:
- Competitors—conduct illicit activities to steal trade secrets or other sensitive corporate information.
- Cyber criminals—primarily motivated by financial gain and use various tactics to steal sensitive data or other valuable assets.
- Hacktivists—seek to disrupt specific organizations for political or social reasons.
- Nation states—target sensitive government data or critical infrastructure.
Key components of cyber risk
The main components of cyber risk are part of threats and include the following.
Capability
Capabilities include the skills, resources, and techniques that a cyber criminal uses to turn a cyber risk into successful exploitation.
Likelihood
After assessing a cyber risk, the chance of it occurring is determined. This likelihood helps categorize and prioritize a cyber risk within the context of other cybersecurity tasks.
Motivation
Understanding the drivers behind a cyber attack can help assess likelihood as well as identify potential targets. As noted above, cyber criminals have varying motivations.
Opportunity
Access potential usually informs opportunity. Whether or not a cyber criminal has or is likely to be able to gain access can help determine the magnitude of cyber risk. Vulnerabilities also offer opportunities for cyber attackers.
Cyber risk management best practices
- Apply a risk-based vulnerability management approach to managing, mitigating, and remediating cyber risks.
- Close any unused accounts.
- Identify and inventory all digital assets and keep the inventory up to date.
- Identify sensitive systems and the potential impact of loss or disruption of those operations if they are damaged or otherwise compromised.
- Monitor access privileges and adjust them to ensure that only the minimum access needed to perform tasks is granted.
- Terminate accounts when users are no longer part of the organization.
- Use machine learning and predictive prioritization tools to identify vulnerabilities and assess their potential impact.
Cyber risk insurance policies
Cyber risk insurance reduces an organization’s exposure through risk transference. Insurance policies help offset any costs associated with a cyber-related incident., such as losses incurred through data destruction, hacking, data extortion, and data theft.
The two types of cyber risk insurance coverage are first-party and third-party. First-party cyber risk insurance covers the costs incurred by the insured organization. Third-party cyber risk insurance helps cover expenses related to damages or losses suffered by third parties, such as customers or vendors.
Coverage and benefits: What to look for
A cyber risk insurance policy should include general coverage for:
- Breach investigation services (e.g., forensic experts)
- Communication support (e.g., public relations or crisis communications specialists)
- Cyber attacks that impact systems
- Data breaches
- Delivery of customer notifications
- Attacks on data stored by vendors and service providers
- Financial compensation for impacted customers
- Legal counsel to help with notifications and other regulatory requirements
- Legal expenses for a lawsuit or regulatory investigation
- Lost or stolen data recovery and replacement
- Penalties or fines related to the cyber incident
- Ransom
- Reimbursement for lost revenue due to operational disruptions
- Settlements related to mediation or lawsuits
Mitigating cyber risk
Three highly effective approaches to mitigating cyber risk are implementing cyber security measures, developing incident response plans, and conducting regular security awareness training.
Cybersecurity measures for vulnerability mitigation
- Asset discovery and inventories
- Attack surface reduction
- Configuration monitoring and management
- Continuous monitoring
- Cyber risk assessments
- Endpoint protection systems
- Security controls (e.g., technical controls, physical access controls, procedural controls, and network access controls)
- Security patch and software update management
- Threat detection systems
- Vulnerability assessments
Incident response and crisis management
- Create a detailed incident response plan to:
- Outline the immediate actions to be taken when an incident occurs
- Establish communication protocols to inform stakeholders
- Define steps for system recovery
- Test and update the incident response plan
- Incorporate lessons learned from past incidents
Cybersecurity awareness and prevention
Regular cybersecurity training plays a key role in reducing cyber risk. These programs should help employees understand:
- Common forms of attacks
- Ways to recognize phishing attempts and other social engineering ploys
- Importance of strong passwords
- Security policies and protocols
Protecting the enterprise from evolving cyber risk
Proactive defense is the best approach to protect the enterprise from evolving cyber risk. IT and security teams need to stay on top of the latest trends in security solutions as well as the threat landscape. Unfortunately, as security advances, so do cyber criminals, who continually evolve attack vectors to evade new security measures.
The evolving threat landscape
Cyber attack trends reflect the evolving threat landscape. Key threats that organizations should be aware of to manage and mitigate cyber risk effectively include the following.
- Artificial intelligence- and machine learning-powered attacks
- Generative AI-powered targeted phishing attacks
- IoT (internet of things) and mobile device vulnerabilities
- Mega attacks
- Quantum computing threats
- Ransomware
- Security skills gap and staffing issues
- Supply chain attacks
- Third-party vendor vulnerabilities
- Zero-day attacks
Advanced technologies and practices
Artificial intelligence is at the heart of most advanced cyber risk management and mitigation solutions and practices. It gives organizations the ability to manage an increasingly complex threat landscape by leveraging the power of machines to process information faster and in ways that humans cannot.
AI tools can collect, aggregate, and correlate threat intelligence to identify and respond to cyber attacks in real time.
AI also can automate responses to new and emerging attacks to mitigate them quickly.
Cyber risk awareness is key
Cyber risk can be found in all areas of an organization. While most cyber risk is associated with IT, it is imperative to have organization-wide awareness of this challenge and its potential impact. Engaging users across the organization helps mitigate cyber risk and create a culture of security that is at the heart of vulnerability mitigation and a proactive security posture.
You might also be interested in:
Assess the strength of your identity security program
Research-backed, industry-specific benchmark data and a roadmap for driving business value